- Alcatel (6)
- Android (6)
- Blogger (10)
- Bluetooth Speakers (1)
- Calculators (1)
- Facebook (1)
- Games (4)
- GitHub (1)
- Html-Css-Js (46)
- Illustrator (2)
- InfoSec (13)
- Photoshop (4)
- PHP (11)
- Unicode (2)
- Windows (2)
jQuery
elevateZoom (Requires jQuery)
Microsoft Store (Donation)
Facebook Messenger (Donation)
Click here to go to this blog's Facebook Page!
Thank you!
Request Web\PHP\JavaScript\HTML Project !
Contact us if you want us to develop a Web\PHP\JavaScript\HTML project for you!
Advertise On This Blog!
If you want a Product\Service\Event to be advertised on this blog, feel free to contact us!
Ads (Reserved)
Thursday, December 16, 2021
Tuesday, December 14, 2021
Saturday, October 30, 2021
The Best Protection For Your Email Account!
Believe it or not, the best protection for your email account is to not make its "main email address" public by any means, only you should know about its existence!
The "main email address" should be used only to login into your email account, never share it with nobody, never use it to sign up or create accounts in websites, etc!
In the other hand, create 1 or multiple "alias email address\es" in your email account and use it\them to share with people, sign up or create accounts in websites, etc!
Finally, always make sure that none of your "alias email addresses" have the permission to login into your email account!
That's it! If hackers don´t know the door to your email account, so they can't try any keys!
Thursday, October 28, 2021
Android - Move Files and Folders Instantly!
The Cut\Paste in the Android built-in file manager is slow! It actually does not "Move" the files\folders, it creates new ones by copy\pasting the old ones to the new location, then it deletes the old ones from the old location!
So basically, Cut\Paste = Copy\Paste\Delete, in Android built-in file manager! (Which is absurd and ridiculous!)
In the other hand, if you want Cut\Paste to move files\folders fast and instantly, you can use 3rd party file manager apps like "FX File Explorer"!
The Cut\Paste from "FX File Explorer" works as intended, it does not create new files\folders, it just changes the location of files\folders that already exist to a new location!
FX File Explorer (Google Play Store)
Wednesday, October 27, 2021
Android - Edit Text Files From SD card!
In several Android phones, 3rd Party Apps like text editors can´t access or edit files from SD cards (External Storage)!
Fortunately, there are 3rd Party Apps like "FX File Explorer" that allows you to access and edit files from SD cards!
In order to be able to "edit" files from SD cards with "FX File Explorer", you need to:
- Open "FX File Explorer", then open "Media Card"
- in "Media Card" press the settings button, then press the "Enable Write Access"
- Now you can edit text files from SD card with "FX File Explorer"
FX File Explorer (Google Play Store)
Tuesday, October 26, 2021
Android - Some Fixes for 3rd Party Alarm Apps Not Going Off On Time or Not Going Off At All!
Best Alarm App for Android! (Click here)
Battery:
- go to settings, then open "Battery"
- disable "Battery Saver", or, if possible, exclude the alarm app if "Battery Saver" is enabled!
- disable "Battery Optimization", or, if possible, exclude the alarm app if "Battery Optimization" is enabled!
- disable "Standby Inteligent Power Saving", or, if possible, exclude the alarm app if "Standby Inteligent Power Saving" is enabled!
Enable Auto-Start:
- go to settings, open "Smart Manager", then open "App Manager"
- allow the alarm app to auto-start
Power Saving:
- go to settings, open "Smart Manager", then open "Power Saving"
- exclude the alarm app from any Optimization options available
Monday, October 25, 2021
Android - Best Alarm App
"Caynax Alarm Clock" is the best alarm app for Android available so far!
- Very well organized
- It shows the time left for each alarm to go off
- Next alarm\s can be skipped
- Multi snooze options available
Caynax Alarm Clock (Free)
Caynax Alarm Clock Pro
Some Fixes for 3rd Party Alarm Apps Not Going Off On Time or Not Going Off At All on Android! (Click Here)
Android - Change Ring Time
Normally, 5 seconds is min and 30 seconds is max! (Depends on the phone carrier!)
Call your phone carrier if you want to set a value higher than the max allowed!)
Disabling "voicemail" and "missed calls sms" may allow ringing duration to go higher than 30/45 seconds!
If you want "missed calls" notification to play ring music from start to end, do it from "Settings\Apps & notifications\Phone\App notifications"!
___________________________________________
To find out your voicemail number and how long your phone is currently ringing before diverting to voicemail, dial:
*#61#
You’ll see a pop-up appear that tells you your voicemail phone number, and how many seconds your phone will ring for each call that comes in.
___
Another way to find voicemail number:
- in dial screen, open "Settings", "Call Settings", then "Call Forwarding"
- In some phones, in "Call Forwarding" option, the ring duration and voicemail number can be changed by using the "When Unanswered" option!
___
Note that, the voicemail number may be different than the phone number, example:
phone number: +238 9348756
voicemail: +238 18 9348756
____________________________________________
To change ringing duration, dial: **61*VoicemailNumber**Seconds#
Example, after dialing *#61#, +238189348756 is returned:
for (15 seconds): **61*+238189348756**15#
for (30 seconds): **61*+238189348756**30#
You’ll then see a pop-up appear with a message that says “Call forwarding successful”!
___________________________________________
Another way is to use: **61*101**Seconds#
for (15 seconds): **61*101**15#
for (30 seconds): **61*101**30#
Make sure to write down your voicemail number first before using this method because it may change your voicemail number to "101"!
If your voicemail number was changed to "101", use the other methods mentioned above to revert it back!
___________________________________________
Friday, October 22, 2021
Image Slider for Blogger
Download "Splide Slider + Examples + How to Notes for Blogger":
https://www.mediafire.com/file/d2z2ymxv4u5z5oj/Splide_Image_Slider_%2528Blogger%2529.rar/file
Monday, May 31, 2021
Monday, May 24, 2021
[JavaScript] Date Time Zone (Function)
Download v1.1 (Changelog Note file included):
https://www.mediafire.com/file/7cia0vmekbkgnsu/Date_Time_Zone%2528Function%2529_-_v1.1.zip/file
Download v1.0:
https://www.mediafire.com/file/8rsq0tzofhgggzv/Date_Time_Zone%2528Function%2529_-_v1.0.html/file
Friday, May 21, 2021
"Password + Passcode" Login! (Passcode-Factor Authentication)
Password Reuse is proving to be a real and a big security problem these days, which is already forcing a lot of websites to implement ridiculous 2FA\MFA security measures! Two-factor or Multi-factor Authentication is a Waste of Time! (Click here to know more!)
The current way 2FA\MFA is being implemented is not the solution for Password Reuse, it's just another problem!
The solution for Password Reuse should\must be simple, practical and safe, thus, we propose a "Passcode-Factor Authentication" (PFA) solution, which would require "Password + Passcode" for users to login into their accounts!
What would be this "Passcode-Factor Authentication"?
Well, password is something that the user can choose, the user chooses whatever password he\she wants, weak, strong, random, reused, etc!
In the other hand, passcode would be something that the user can't choose, it should\must be a "Strong Long Random Code" generated by the website itself!
Then, both "Password + Passcode" would be required for users to login into their accounts, to change account settings, etc!
With this "Passcode-Factor Authentication" implemented, a Website should\must recommend its users to store the passcodes into a password manager!
The website should also recommend its users to use "Strong Long Random Passwords" by using their password manager's password generator and to never reuse passwords! (Strong Long Random Password + Strong Long Random Code = Hackproof)
This way, "Passcode-Factor Authentication" would prevent hackers to login into users accounts with reused passwords found in other websites data breaches!
Almost all accounts are hacked because of Password Reuse, thus, a simple solution like "Passcode-Factor Authentication" would be enough! Proposed solutions like 2FA Authenticator apps with 30 seconds input limit are neither simple, practical nor safe solutions, so almost all people will keep rejecting them!
2FA\MFA solutions that force people to be chained\dependent to emails, sms, authenticator apps\devices, etc, should\must be avoided at all cost!
Monday, May 3, 2021
[JavaScript] Get TimeZone Name (Function)
Unfortunately, none of the functions below work with Internet Explorer! (The previous statement that one of the functions works with IE11 was wrong!)
v1.2 (Changelog Note file included):
https://www.mediafire.com/file/0tmn6o78pal8r38/Get_TimeZone_Name%2528Function%2529_-_v1.2.zip/file
v1.1 ("Date_String" parameter added):
https://www.mediafire.com/file/6hy14nh2hkiqfes/Get_TimeZone_Name%2528Function%2529_-_v1.1.rar/file
Saturday, May 1, 2021
Two-factor or Multi-factor Authentication is a Waste of Time!
The image above basically says it all, Two-factor or Multi-factor Authentication is just a Waste of Time!
Instead of complicating and wasting time with 2, 3, 4, 1000, Multi or Infinite-factor Authentication, we must keep things as simple as possible, we need to make a strong and secure "One-factor Authentication", or, 1FA, if you prefer!
In order to use a strong and secure "One-factor Authentication" (1FA), you just need to use a real password manager like Multi One Password (Click here), a password manager that does not store passwords neither locally in the users devices nor in the cloud! (Note that, almost all password managers available out there are not really password managers, they are Note managers!)
Saying that, let's go back to Two-factor or Multi-factor Authentication, some big companies, like Google for example, are trying to make them standard since 2009 or 2010, but still almost all people refuse to use them because they bring too much unnecessary problems and headaches, and they are absolutely right for not using them!
As already said above, these big companies have been putting big money in 2FA/MFA since 2009/2010, now they want "Return on Investment" (ROI), so they want to force 2FA/MFA on everybody, even though 2FA/MFA is proving to be a Waste of Time and a Big Failure!
2FA/MFA is not the answer! If hackers can steal your passwords, they can steal your 2FA/MFA information as well!
There are a lot of people living nightmares because they decided to use 2FA/MFA, and now they regret for doing it so!
2FA/MFA makes use of backup codes! Backup codes can either be stolen or breached, thus, 2FA/MFA is just an extra headache that causes a lot of unnecessary problems!
If hackers ask you for your passwords and you give them your passwords, they will also ask you for your 2FA/MFA backup codes and you will give them the backup codes!
If Passwords can be breached from servers, 2FA/MFA backup codes can also be breached from servers!
If a data breach from a server contains passwords, it will certainly contain 2FA/MFA backup codes as well!
A data breach can also contain active-sessions, active-logged-in-devices, etc data, and hackers can use them to bypass 2FA\MFA as well!
If you use public wifi\wired networks with some frequency, hackers could easily intercept the data your devices send\receive in the network (cookies, active-session, etc) and use that data to bypass 2FA\MFA! (Especially public wifi networks that don't require passwords to access)
Websites decide if backup codes are used or not, and almost all of them use backup codes for their 2FA/MFA implementation, and if they don't, pray to GODS to never lose your 2FA/MFA devices or physical keys, because if you do, well, you must prepare yourself to live Nightmares after Nightmares, being locked from your accounts for 1, 2, 3 or even more months/years, and like in many cases, For Ever!
"Passcode-Factor Authentication", a Perfect Solution for Password Reuse! (Click Here)
Friday, March 26, 2021
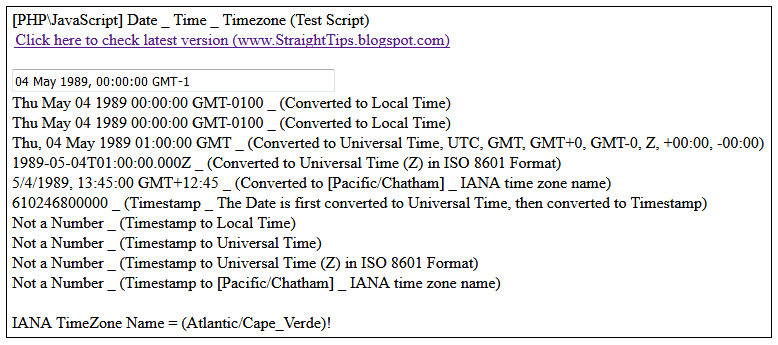
[PHP\JavaScript] Date, Time and Timezone (Test Script)
(Type\Paste a "Date" or "Timestamp" in the input box above!)
IANA TimeZone Name = ()!
Timezone Offset = minutes! (Timezone Offset / -60 = )
Download the complete php\javascript script from the video here (v1.1):
https://www.mediafire.com/file/g3454kwh1lyttzi/PHP-JavaScript_-_Date-Time-Timezone_%2528v1.1%2529.php/file
(v1.1) Change Log:
- [hourCycle:"h12"] in use instead [hour12:true]
- [hourCycle:"h23"] in use instead [hour12:false]
(v1.0):
https://www.mediafire.com/file/r1diygunxqgkc2g/PHP-JavaScript_-_Date-Time-Timezone_%2528v1.0%2529.php/file
Keywords:
#php #JavaScript #html #css #Timezone #date #time #utc #gmt #iso8601
Tuesday, February 2, 2021
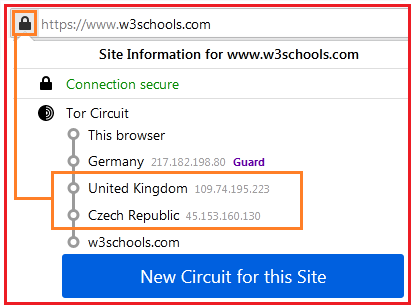
[Tor] Create "New Circuit" for a Domain at every given time!
First of all, the code to create a "New Tor Circuit" for a domain was found in the gitlab page of Tor! (See line 516 <Click Here>)
Secondly, the code only works in "Browser" console (Shift + Ctrl + j), it does not work neither in "<script>" tag nor in "Web" console (Shift + Ctrl + k)!
Thirdly, in order to run codes in "Browser" console, "devtools.chrome.enabled" from "about:config" must be set to "true"! (See the image above for more details!)
Below is the code to Create "New Tor Circuit" for a given domain:
Change "w3schools.com" to any other domain you want! (It must be "Domain.com", not "www.Domain.com"! For example, "www.w3schools.com" does not work!)
After executing the code, open "w3schools.com" in a new "tab", or just reload the current open tab, and you will notice that the "Tor circuit" was changed!
Wednesday, January 20, 2021
DDOS with File Upload?
Login DDoS?
Is it possible to DDOS by uploading files, logging-in, sending posts, sending emails, searching or just by sending multiple Http requests to websites?
Download the files from the videos and do your own tests!
Use at your own risk! (This is mainly to be used by developers on their own websites!)
v1.2:
https://www.mediafire.com/file/o15geddihh2bdjy/DDOS_File_Upload_%2528v1.2%2529.rar/file
v1.2:
- "Every" option added! (Send x number of "Request\s" at every given time!)
- "Server Response Timeout" option added!
- Some infos and codes related to "Freeing Ram Memory" added!
- "Response Text Contains" added! (Informs if a server response contains words such as "Cloudflare", "Access denied", "rate limit", etc!)
v1.1:
- "Repeat" option added! (When a "request" terminates, a new "request" initiates!)
Keywords:
#html #css #javascript #php #dos #ddos
Saturday, January 16, 2021
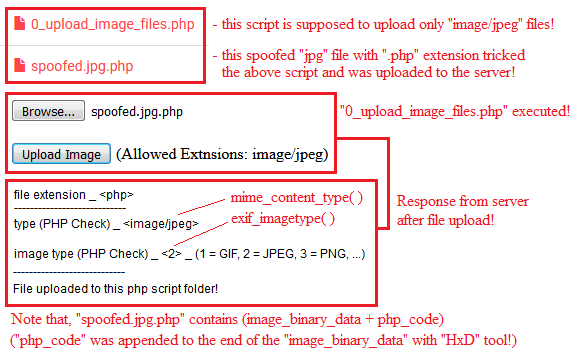
[PHP] Upload Spoofed Files
"spoofed.jpg.php" is a spoofed "jpg" file with a "php" code appended at the end of the image-binary-data with "HxD" binary\hex editor tool!
Extension check is useful to prevent files to be stored in the server with dangerous extensions such as ".php,.xml,.html, etc"!
"mime_content_type" and "exif_imagetype" should be used for identification purposes only, not for security purposes!
The above functions should not be used for security purposes because both of them allow spoofed files!
A spoofed file is, for example, a "jpg" image file with a "php" code appended at the end of the image-binary-data!
This page just demonstrates a simple example on how it's dangerous to use "$_FILES['file']['name']" with "mime_content_type" or "exif_imagetype" functions!
Download the files below and do your own tests:
https://www.mediafire.com/file/zm9q2a7uoel2zn9/PHP_-_Upload_Spoofed_Files.rar/file