- Alcatel (6)
- Android (6)
- Blogger (10)
- Bluetooth Speakers (1)
- Calculators (1)
- Facebook (1)
- Games (4)
- GitHub (1)
- Html-Css-Js (46)
- Illustrator (2)
- InfoSec (13)
- Photoshop (4)
- PHP (11)
- Unicode (2)
- Windows (2)
jQuery
elevateZoom (Requires jQuery)
Microsoft Store (Donation)
Facebook Messenger (Donation)
Click here to go to this blog's Facebook Page!
Thank you!
Request Web\PHP\JavaScript\HTML Project !
Contact us if you want us to develop a Web\PHP\JavaScript\HTML project for you!
Advertise On This Blog!
If you want a Product\Service\Event to be advertised on this blog, feel free to contact us!
Ads (Reserved)
Friday, March 26, 2021
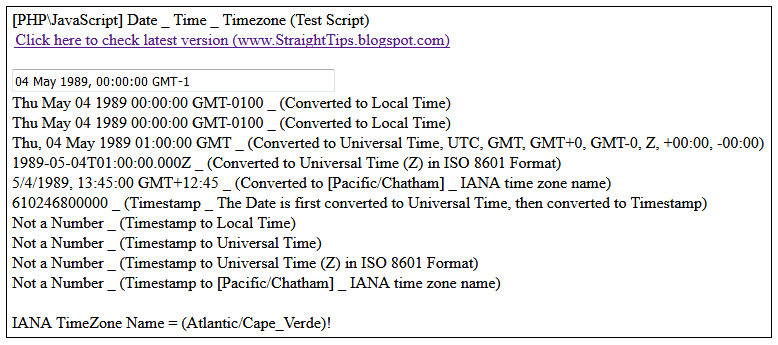
[PHP\JavaScript] Date, Time and Timezone (Test Script)
(Type\Paste a "Date" or "Timestamp" in the input box above!)
IANA TimeZone Name = ()!
Timezone Offset = minutes! (Timezone Offset / -60 = )
Download the complete php\javascript script from the video here (v1.1):
https://www.mediafire.com/file/g3454kwh1lyttzi/PHP-JavaScript_-_Date-Time-Timezone_%2528v1.1%2529.php/file
(v1.1) Change Log:
- [hourCycle:"h12"] in use instead [hour12:true]
- [hourCycle:"h23"] in use instead [hour12:false]
(v1.0):
https://www.mediafire.com/file/r1diygunxqgkc2g/PHP-JavaScript_-_Date-Time-Timezone_%2528v1.0%2529.php/file
Keywords:
#php #JavaScript #html #css #Timezone #date #time #utc #gmt #iso8601
Tuesday, February 2, 2021
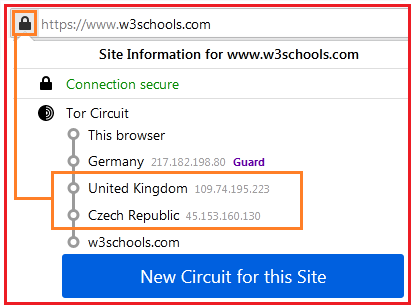
[Tor] Create "New Circuit" for a Domain at every given time!
First of all, the code to create a "New Tor Circuit" for a domain was found in the gitlab page of Tor! (See line 516 <Click Here>)
Secondly, the code only works in "Browser" console (Shift + Ctrl + j), it does not work neither in "<script>" tag nor in "Web" console (Shift + Ctrl + k)!
Thirdly, in order to run codes in "Browser" console, "devtools.chrome.enabled" from "about:config" must be set to "true"! (See the image above for more details!)
Below is the code to Create "New Tor Circuit" for a given domain:
Change "w3schools.com" to any other domain you want! (It must be "Domain.com", not "www.Domain.com"! For example, "www.w3schools.com" does not work!)
After executing the code, open "w3schools.com" in a new "tab", or just reload the current open tab, and you will notice that the "Tor circuit" was changed!
Wednesday, January 20, 2021
DDOS with File Upload?
Login DDoS?
Is it possible to DDOS by uploading files, logging-in, sending posts, sending emails, searching or just by sending multiple Http requests to websites?
Download the files from the videos and do your own tests!
Use at your own risk! (This is mainly to be used by developers on their own websites!)
v1.2:
https://www.mediafire.com/file/o15geddihh2bdjy/DDOS_File_Upload_%2528v1.2%2529.rar/file
v1.2:
- "Every" option added! (Send x number of "Request\s" at every given time!)
- "Server Response Timeout" option added!
- Some infos and codes related to "Freeing Ram Memory" added!
- "Response Text Contains" added! (Informs if a server response contains words such as "Cloudflare", "Access denied", "rate limit", etc!)
v1.1:
- "Repeat" option added! (When a "request" terminates, a new "request" initiates!)
Keywords:
#html #css #javascript #php #dos #ddos
Saturday, January 16, 2021
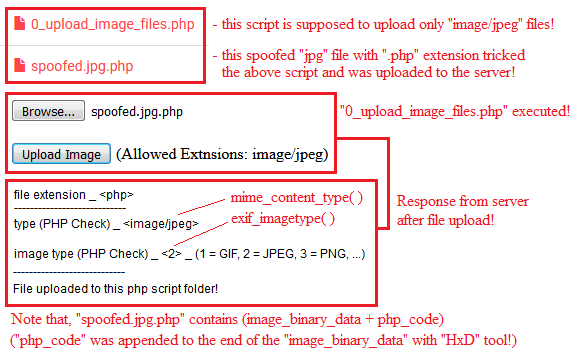
[PHP] Upload Spoofed Files
"spoofed.jpg.php" is a spoofed "jpg" file with a "php" code appended at the end of the image-binary-data with "HxD" binary\hex editor tool!
Extension check is useful to prevent files to be stored in the server with dangerous extensions such as ".php,.xml,.html, etc"!
"mime_content_type" and "exif_imagetype" should be used for identification purposes only, not for security purposes!
The above functions should not be used for security purposes because both of them allow spoofed files!
A spoofed file is, for example, a "jpg" image file with a "php" code appended at the end of the image-binary-data!
This page just demonstrates a simple example on how it's dangerous to use "$_FILES['file']['name']" with "mime_content_type" or "exif_imagetype" functions!
Download the files below and do your own tests:
https://www.mediafire.com/file/zm9q2a7uoel2zn9/PHP_-_Upload_Spoofed_Files.rar/file
Thursday, December 17, 2020
[PHP] Password, Passcode and Passcookie!
Download v1.2:
https://www.mediafire.com/file/bhxcfopuntivnil/PHPppp_%2528v1.2%2529.zip/file
v1.2 - User Management (Change User, Level and Permissions):
v1.1 - Create Account:
v1.0:
Keywords:
PHP Password Passcode Passcookie
JavaScript HTML
Tuesday, November 24, 2020
[PHP] wait_Read_Write_end_of($File) Functions
To avoid the above problem, PHP "flock()" function must be used! In order to automate all the process, "wait_Write_end_of()" function can be used, as it makes use of "flock()" function!
Multiple processes writing at same time to a file, can cause all kind of problems we can imagine, thus, the "flock()" function must also be used here! In order to automate all the process, "wait_Read_Write_end_of()" function can be used, as it makes use of "flock()" function as well!
"wait_Write_end_of($File)", Read a file if the file is not being written! (If the file is being written, the execution is halted until the file is unlocked!)
"wait_Read_Write_end_of($File)", Write to a file if the file is not being read or written! (If the file is being read or written, the execution is halted until the file is unlocked!)
One minor thing to be noted is that "flock()" does not handle the requests in order of call!
The code below can be used to test how PHP handles Read\Write requests!
Test Notes:
- while "LOCK_EX Write" button is writing to file, "Read" button incorrectly returns empty file content!
- while "LOCK_EX Write" button is writing to file, "LOCK_SH Read" button returns the correct file content!
- for File content = "Oops_":
- if, for example, "Write" button is pressed 5 times at once, it incorrectly writes "zops_z" instead "Oops_yyyyz" to the file!
- if, for example, "LOCK_EX Write" button is pressed 5 times at once, it correctly writes "Oops_wwwwx" to the file as expected!